State of Application Security Vol. 4
•
62 gostaram•5,250 visualizações
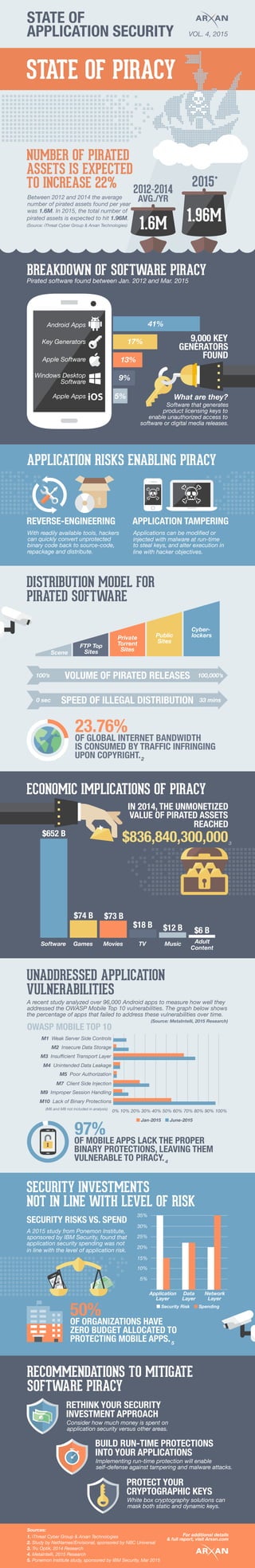
Arxan Technologies inforgraphic on the current state of application security.
Denunciar
Compartilhar
Denunciar
Compartilhar
Baixar para ler offline
Recomendados
Briskinfosec - Threatsploit Report Augest 2021- Cyber security updates

Briskinfosec - Threatsploit Report Augest 2021- Cyber security updatesBriskinfosec Technology and Consulting
Mais conteúdo relacionado
Mais procurados
Briskinfosec - Threatsploit Report Augest 2021- Cyber security updates

Briskinfosec - Threatsploit Report Augest 2021- Cyber security updatesBriskinfosec Technology and Consulting
Mais procurados (20)
Mobile Security: Perceptions vs Device-harvested Reality

Mobile Security: Perceptions vs Device-harvested Reality
Top 2016 Mobile Security Threats and your Employees

Top 2016 Mobile Security Threats and your Employees
Symantec Internet Security Threat Report 2014 - Volume 19

Symantec Internet Security Threat Report 2014 - Volume 19
Looking Forward and Looking Back: Lookout's Cybersecurity Predictions

Looking Forward and Looking Back: Lookout's Cybersecurity Predictions
Feds: You have a BYOD program whether you like it or not

Feds: You have a BYOD program whether you like it or not
Deutsche Telekom Partnering Operating Alliance Summit - Zimperium

Deutsche Telekom Partnering Operating Alliance Summit - Zimperium
Malware on Smartphones and Tablets: The Inconvenient Truth

Malware on Smartphones and Tablets: The Inconvenient Truth
Mobile Security: The 5 Questions Modern Organizations Are Asking

Mobile Security: The 5 Questions Modern Organizations Are Asking
Briskinfosec - Threatsploit Report Augest 2021- Cyber security updates

Briskinfosec - Threatsploit Report Augest 2021- Cyber security updates
Five mobile security challenges facing the enterprise

Five mobile security challenges facing the enterprise
Destaque
The Inmates Are Running the Asylum: Why Some Multi-Factor Authentication Tech...

The Inmates Are Running the Asylum: Why Some Multi-Factor Authentication Tech...Clare Nelson, CISSP, CIPP-E
Destaque (20)
MATATABI: Cyber Threat Analysis and Defense Platform using Huge Amount of Dat...

MATATABI: Cyber Threat Analysis and Defense Platform using Huge Amount of Dat...
Balancing Mobile UX & Security: An API Management Perspective Presentation fr...

Balancing Mobile UX & Security: An API Management Perspective Presentation fr...
Data Security and Privacy by Contract: Hacking Us All Into Business Associate...

Data Security and Privacy by Contract: Hacking Us All Into Business Associate...
To Serve and Protect: Making Sense of Hadoop Security 

To Serve and Protect: Making Sense of Hadoop Security
PSFK Presents the Future of Digital Safety & Security

PSFK Presents the Future of Digital Safety & Security
Pivotal Digital Transformation Forum: Accelerate Time to Market with Business...

Pivotal Digital Transformation Forum: Accelerate Time to Market with Business...
Pivotal Digital Transformation Forum: Becoming a Data Driven Enterprise

Pivotal Digital Transformation Forum: Becoming a Data Driven Enterprise
Pivotal Digital Transformation Forum: Data Science 

Pivotal Digital Transformation Forum: Data Science
Hivemall: Scalable machine learning library for Apache Hive/Spark/Pig

Hivemall: Scalable machine learning library for Apache Hive/Spark/Pig
The Inmates Are Running the Asylum: Why Some Multi-Factor Authentication Tech...

The Inmates Are Running the Asylum: Why Some Multi-Factor Authentication Tech...
Semelhante a State of Application Security Vol. 4
Semelhante a State of Application Security Vol. 4 (20)
Protect Your Enterprise - Check Point SandBlast Mobile

Protect Your Enterprise - Check Point SandBlast Mobile
Presentatie Kaspersky over Malware trends en statistieken, 26062015

Presentatie Kaspersky over Malware trends en statistieken, 26062015
Mobile Payments: Protecting Apps and Data from Emerging Risks

Mobile Payments: Protecting Apps and Data from Emerging Risks
Mobile Application Security Testing, Testing for Mobility App | www.idexcel.com

Mobile Application Security Testing, Testing for Mobility App | www.idexcel.com
apidays LIVE New York 2021 - Playing with FHIR without getting burned by Dav...

apidays LIVE New York 2021 - Playing with FHIR without getting burned by Dav...
What the New OWASP Top 10 2013 and Latest X-Force Report Mean for App Sec

What the New OWASP Top 10 2013 and Latest X-Force Report Mean for App Sec
apidays LIVE LONDON - API Abuse - Comprehension and Prevention by David Stewart

apidays LIVE LONDON - API Abuse - Comprehension and Prevention by David Stewart
application-security-fallacies-and-realities-veracode

application-security-fallacies-and-realities-veracode
Black Duck & IBM Present: Application Security in the Age of Open Source

Black Duck & IBM Present: Application Security in the Age of Open Source
Mais de IBM Security
Mais de IBM Security (20)
Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...

Leaders & Laggards: The Latest Findings from the Ponemon Institute’s Study on...
Bridging the Gap between Privacy and Security: Using Technology to Manage Com...

Bridging the Gap between Privacy and Security: Using Technology to Manage Com...
The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...

The Resilient End-of-Year Review: The Top Cyber Security Trends in 2018 and P...
Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...

Leveraging Validated and Community Apps to Build a Versatile and Orchestrated...
Accelerating SOC Transformation with IBM Resilient and Carbon Black

Accelerating SOC Transformation with IBM Resilient and Carbon Black
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
Último
Último (20)
Time Series Foundation Models - current state and future directions

Time Series Foundation Models - current state and future directions
Modern Roaming for Notes and Nomad – Cheaper Faster Better Stronger

Modern Roaming for Notes and Nomad – Cheaper Faster Better Stronger
Take control of your SAP testing with UiPath Test Suite

Take control of your SAP testing with UiPath Test Suite
Scale your database traffic with Read & Write split using MySQL Router

Scale your database traffic with Read & Write split using MySQL Router
Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: Loan Stars - Tech Forum 2024
Generative Artificial Intelligence: How generative AI works.pdf

Generative Artificial Intelligence: How generative AI works.pdf
Testing tools and AI - ideas what to try with some tool examples

Testing tools and AI - ideas what to try with some tool examples
The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx

The Role of FIDO in a Cyber Secure Netherlands: FIDO Paris Seminar.pptx
Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...

Unleashing Real-time Insights with ClickHouse_ Navigating the Landscape in 20...
Long journey of Ruby standard library at RubyConf AU 2024

Long journey of Ruby standard library at RubyConf AU 2024
How AI, OpenAI, and ChatGPT impact business and software.

How AI, OpenAI, and ChatGPT impact business and software.
So einfach geht modernes Roaming fuer Notes und Nomad.pdf

So einfach geht modernes Roaming fuer Notes und Nomad.pdf
(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...

(How to Program) Paul Deitel, Harvey Deitel-Java How to Program, Early Object...
State of Application Security Vol. 4
- 1. STATE OF APPLICATION SECURITY VOL. 4, 2015 STATE OF PIRACY 1.6M 1.96M ASSETS IS EXPECTED NUMBER OF PIRATED Pirated software found between Jan. 2012 and Mar. 2015 BREAKDOWN OF SOFTWARE PIRACY Between 2012 and 2014 the average Android Apps Key Generators Apple Software Windows Desktop Software Apple Apps number of pirated assets found per year 2012-2014 AVG./YR 2015* was 1.6M. In 2015, the total number of 41% 17% 13% 9% 5% KEY9,000 GENERATORS FOUND Software that generates product licensing keys to enable unauthorized access to software or digital media releases. What are they? APPLICATION RISKS ENABLING PIRACY DISTRIBUTION MODEL FOR REVERSE-ENGINEERING APPLICATION TAMPERING With readily available tools, hackers can quickly convert unprotected binary code back to source-code, repackage and distribute. VOLUME OF PIRATED RELEASES SPEED OF ILLEGAL DISTRIBUTION 100’s 100,000’s 0 sec 33 mins Scene FTP Top Sites Private Torrent Sites Public Sites Cyber- lockers Applications can be modified or injected with malware at run-time to steal keys, and alter execution in line with hacker objectives. 23.76% OF GLOBAL INTERNET BANDWIDTH IS CONSUMED BY TRAFFIC INFRINGING UPON COPYRIGHT. ECONOMIC IMPLICATIONS OF PIRACY 2 pirated assets is expected to hit 1.96M. (Source: iThreat Cyber Group & Arxan Technologies) TO INCREASE 22% PIRATED SOFTWARE IN 2014, THE UNMONETIZED VALUE OF PIRATED ASSETS REACHED $836,840,300,000$652 B $74 B $73 B $18 B $12 B $6 B Software Games Movies TV Music Adult Content UNADDRESSED APPLICATION VULNERABILITIES M1 Weak Server Side Controls M2 Insecure Data Storage M3 Insufficient Transport Layer M4 Unintended Data Leakage M5 Poor Authorization M7 Client Side Injection M9 Improper Session Handling M10 Lack of Binary Protections 0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100% Jan-2015 June-2015 OWASP MOBILE TOP 10 97% OF MOBILE APPS LACK THE PROPER BINARY PROTECTIONS, LEAVING THEM VULNERABLE TO PIRACY. 50% OF ORGANIZATIONS HAVE ZERO BUDGET ALLOCATED TO PROTECTING MOBILE APPS. (M6 and M8 not included in analysis) A recent study analyzed over 96,000 Android apps to measure how well they addressed the OWASP Mobile Top 10 vulnerabilities. The graph below shows the percentage of apps that failed to address these vulnerabilities over time. RECOMMENDATIONS TO MITIGATE SOFTWARE PIRACY 35% 30% 25% 20% 15% 10% 5% Application Layer Data Layer Network Layer RETHINK YOUR SECURITY INVESTMENT APPROACH Consider how much money is spent on application security versus other areas. BUILD RUN-TIME PROTECTIONS INTO YOUR APPLICATIONS Implementing run-time protection will enable self-defense against tampering and malware attacks. Security Risk Spending A 2015 study from Ponemon Institute, sponsored by IBM Security, found that application security spending was not PROTECT YOUR CRYPTOGRAPHIC KEYS White box cryptography solutions can mask both static and dynamic keys. SECURITY RISKS VS. SPEND (Source: MetaIntelli, 2015 Research) Sources: 1. iThreat Cyber Group & Arxan Technologies 2. Study by NetNames/Envisional, sponsored by NBC Universal 3. Tru Optik, 2014 Research 4. MetaIntelli, 2015 Research 5. Ponemon Institute study, sponsored by IBM Security, Mar 2015 3 4 5 SECURITY INVESTMENTS NOT IN LINE WITH LEVEL OF RISK in line with the level of application risk. For additional details & full report, visit Arxan.com
